{
"id":"CVE-2021-23214",
"is_known_exploited_vuln":false,
"description":"When the server is configured to use trust authentication with a clientcert requirement or to use cert authentication, a man-in-the-middle attacker can inject arbitrary SQL queries when a connection is first established, despite the use of SSL certificate verification and encryption.",
"urls":[
"https://nvd.nist.gov/vuln/detail/CVE-2021-23214",
"https://git.postgresql.org/gitweb/?p=postgresql.git;a=commit;h=28e24125541545483093819efae9bca603441951",
"https://www.postgresql.org/support/security/CVE-2021-23214/",
"https://github.com/postgres/postgres/commit/28e24125541545483093819efae9bca603441951",
"https://bugzilla.redhat.com/show_bug.cgi?id=2022666"
]
}{
"id":"CVE-2021-23222",
"is_known_exploited_vuln":false,
"description":"A man-in-the-middle attacker can inject false responses to the client's first few queries, despite the use of SSL certificate verification and encryption.",
"urls":[
"https://nvd.nist.gov/vuln/detail/CVE-2021-23222",
"https://github.com/postgres/postgres/commit/160c0258802d10b0600d7671b1bbea55d8e17d45",
"https://git.postgresql.org/gitweb/?p=postgresql.git;a=commitdiff;h=d83cdfdca9d918bbbd6bb209139b94c954da7228",
"https://www.postgresql.org/support/security/CVE-2021-23222/",
"https://bugzilla.redhat.com/show_bug.cgi?id=2022675"
]
}
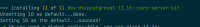
Finally i think we should have slots per every supported and maintained version by Postgresql.
Now active version we have :
Supported Versions:
- Current (14)
- 13
- 12
- 11
- 10
Rest slots are deprecated
Mechanism that same as in php.
Based on webside in this days autogen should produce ebuild for this version
- 14.2,
- 13.6,
- 12.10,
- 11.15,
- 10.20
P.S.
Based on
The lower versions of postgres in our tree are also not updated for CVE